Complete Monitoring Operations in a Single Platform
Every function required to operate an electronic monitoring program — from subject enrollment to violation resolution — unified within one institutional-grade environment.
Continuous Location Monitoring With Intelligent Geofencing
Inclusion zones
Exclusion zones
Schedule-based rules
Corridor zones
Dynamic zones
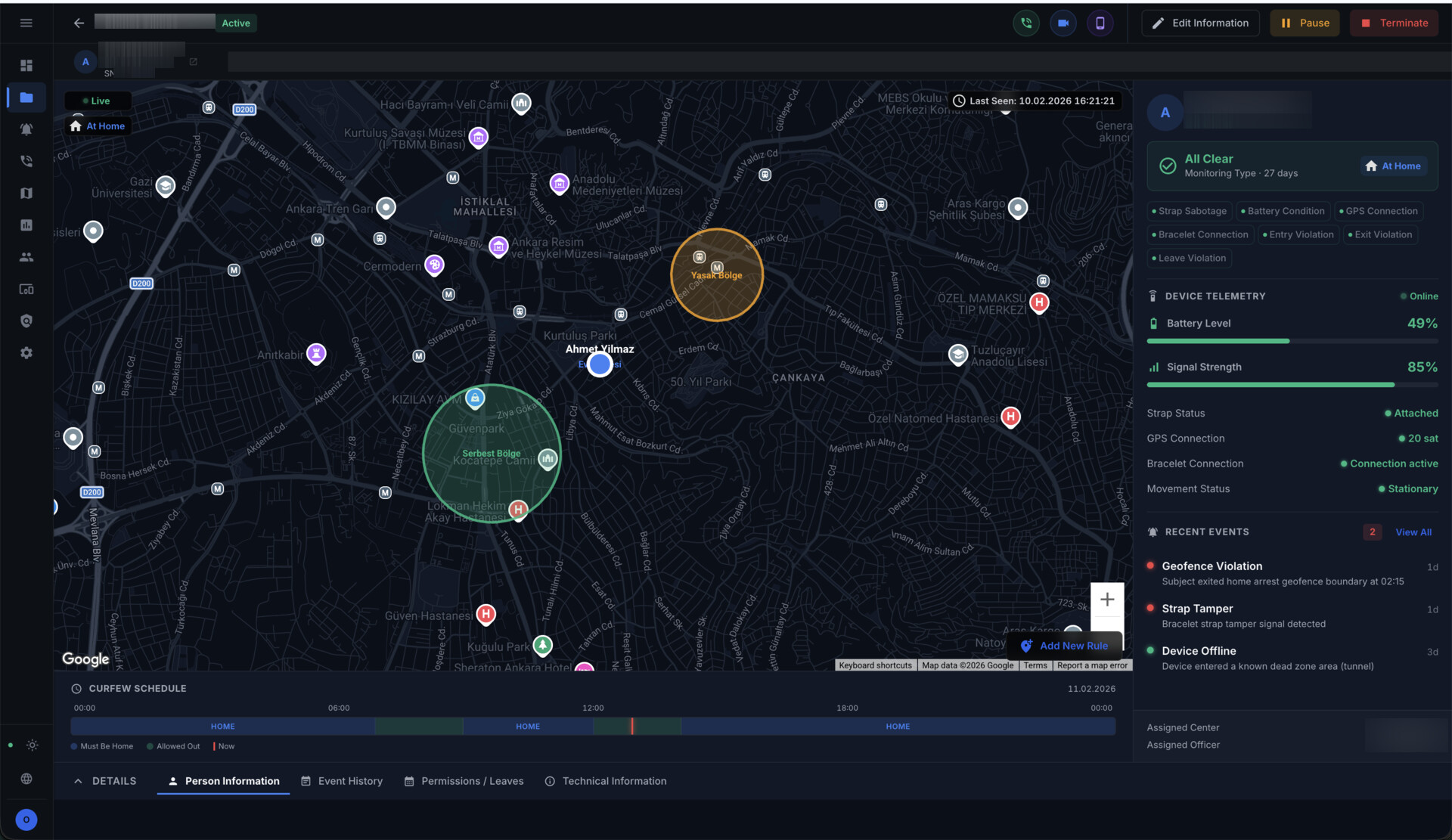
Automated Detection. Structured Escalation. Complete Audit Trails.
- Automatic violation detection
- Severity classification and prioritization
- Operator assignment and escalation workflows
- Resolution documentation with timestamps
- Full event history for each subject
- Exportable violation reports for judicial review
Direct Voice Communication With Monitored Subjects
- Compliance check calls
- Violation response communication
- Scheduled welfare checks
- Emergency contact
Full Device Lifecycle Control
- Device registration and cataloging
- Health status monitoring
- Assignment tracking
- Recovery and return processing
- Maintenance scheduling
- Decommissioning and disposal records
Operational Intelligence for Program Management
01
Daily operations summary02
Subject compliance status03
Violation statistics and trends04
Device utilization and health reports05
Operator activity logs06
Program-level performance metricsInstitutional-Grade Monitoring Without Dedicated Hardware
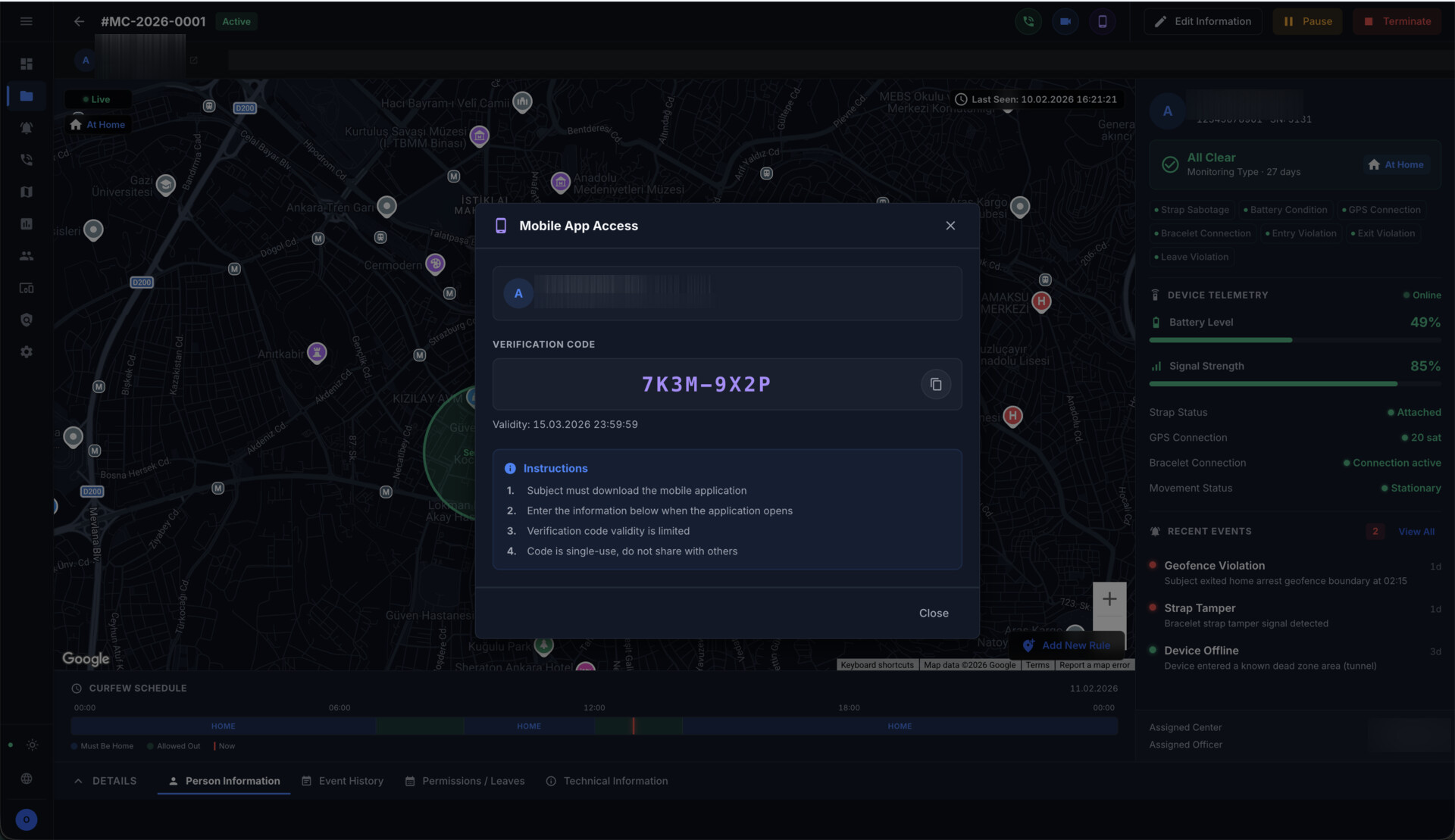
The secure mobile monitoring mode extends the platform's operational reach to subjects who do not require dedicated monitoring hardware.
This is not a consumer tracking application. It is an institutional supervision tool designed for the operational requirements of probation authorities and justice institutions.
- Continuous or scheduled location reporting
- Geofencing and zone enforcement
- Integrity-aware design with behavioral and anomaly detection
- Complete audit trails
- Scalable enrollment without hardware logistics
- Mixed program operations with device-monitored subjects
Role-Based Access for Institutional Security
- Role-based permissions
- Multi-center management
- User activity logging and audit trails
- System configuration and rule management
- Integration settings for external systems